- +65 6397 5396 / 6397 5523
- sales@vgctechnology.com
2023 identity security trends and solutions from Microsoft

- February 3, 2023
- 5:07 am
A version of this article was first published on the Microsoft blog.
Simone Curzi Principal Consultant, Cybersecurity
Welcome to 2023! I wanted to kick this year off by having a quick look at the trends in identity security, what you can do about it, and what Microsoft is doing to help you. One of the things we talk about on the team is “shiny object syndrome”—
Attackers will innovate—
Pamela Dingle gave a keynote at Authenticate 2022 in which she discussed identity attacks in terms of waves (and has recapped on LinkedIn—

This is an awesome frame for thinking through the attacks, so we’ll use it here to complement her blog with concrete features and guidance. I am adding one more threat to her framework—
Password attacks
Simple password attacks are pervasive. They are the water we swim in. I detail these extensively in “Your Password Doesn’t Matter.” The dominant three attacks are:
- Password spray: Guessing common passwords against many accounts.
- Phishing: Convincing someone to type in their credentials at a fake website or in response to a text or email.
- Breach replay: Relying on pervasive password reuse to take passwords compromised on one site and try them against others.
These attacks are effectively free to execute on a massive scale. As a result, Microsoft deflects more than 1,000 password attacks per second in our systems, and more than 99.9 percent of accounts that are compromised don’t have multifactor authentication enabled. Multifactor authentication is one of the most basic defenses against identity attacks today, and despite relentlessly advocating multifactor authentication usage for the past six years, including it in every flavor of Microsoft Azure Active Directory (Azure AD), and innovating in mechanisms from Microsoft Authenticator to FIDO, only 28 percent of users last month had any multifactor authentication session. With such low coverage, attackers increase their attack rate to get what they want. The adoption rate is a demonstration of a critical issue I will return to in this blog—
Driving more multifactor authentication usage is the most important thing we can do for the ecosystem, and if you aren’t yet requiring multifactor authentication for all users, enable it. Old-fashioned, bolt-on multifactor authentication was clunky, requiring copying codes from phone to computer and getting multiple prompts. Modern multifactor authentication using apps, tokens, or the device itself is very low friction or even invisible to the users. Old-fashioned multifactor authentication had to be bought and deployed separately and at additional cost. Modern multifactor authentication is included in all SKUs, deeply integrated into Azure AD, and requires no additional management.
Our strong position is that all user sessions should be multifactor authentication protected, and we are doing all we can to get there. This is why all new tenants created since 2019 have multifactor authentication enabled by default, and why we are now turning on multifactor authentication on behalf of tenants who have not demonstrated interest in their security settings.
Multifactor authentication attacks
If you have enabled multifactor authentication, you can pat yourself on the back and be happy that you’ve effectively deflected the dominant identity attacks. While still far less than the 100 percent we are striving for, the 28 percent of users who are now protected with multifactor authentication include some who are targets for attackers. To get to these targets, attackers have to attack multifactor authentication itself.
Examples here include:
- SIM-jacking and other telephony vulnerability attacks (why we’re asking you to hang up on telephony multifactor authentication).
- Multifactor authentication hammering or griefing attacks, which is why we’re asking you to move away from simple approvals.
- Adversary-in-the-middle attacks, which trick users into doing the multifactor authentication interaction. This is why phishing-resistant authentication is critical, especially for key assets.
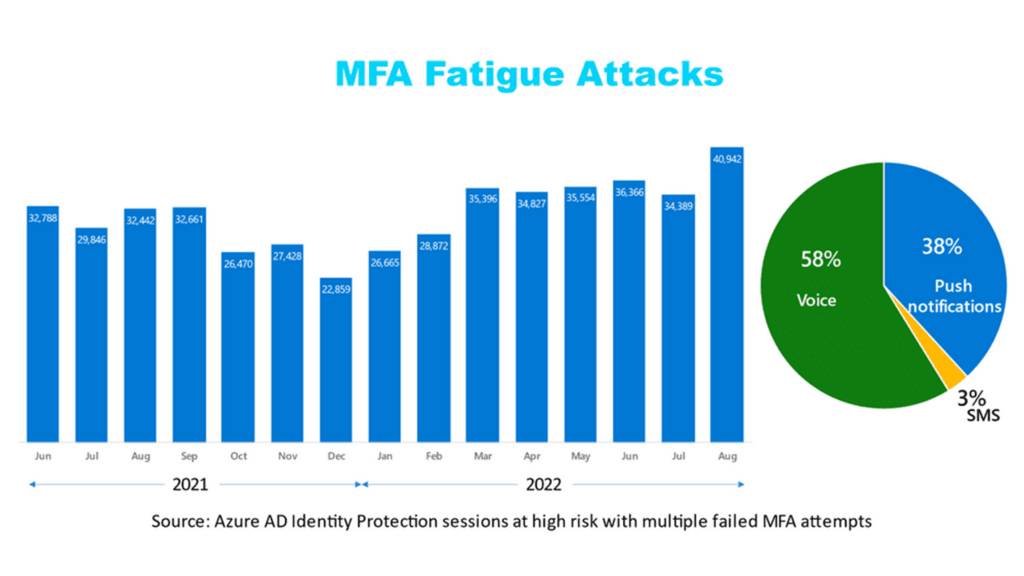
Note these attacks require more effort and attacker investment, and as a result are detected in the tens of thousands per month—
To defeat these attacks, it is critical not just to use multifactor authentication, but to use the right multifactor authentication. We recommend Authenticator, Windows Hello, and FIDO. For organizations with existing personal identity verification card and common access card (PIV and CAC) infrastructure, certificate-based authentication (CBA) is a good phishing-resistant (and executive order-compliant) solution. Bonus: All of these methods are considerably easier to use than passwords or telephony-based multifactor authentication.
Post-authentication attacks
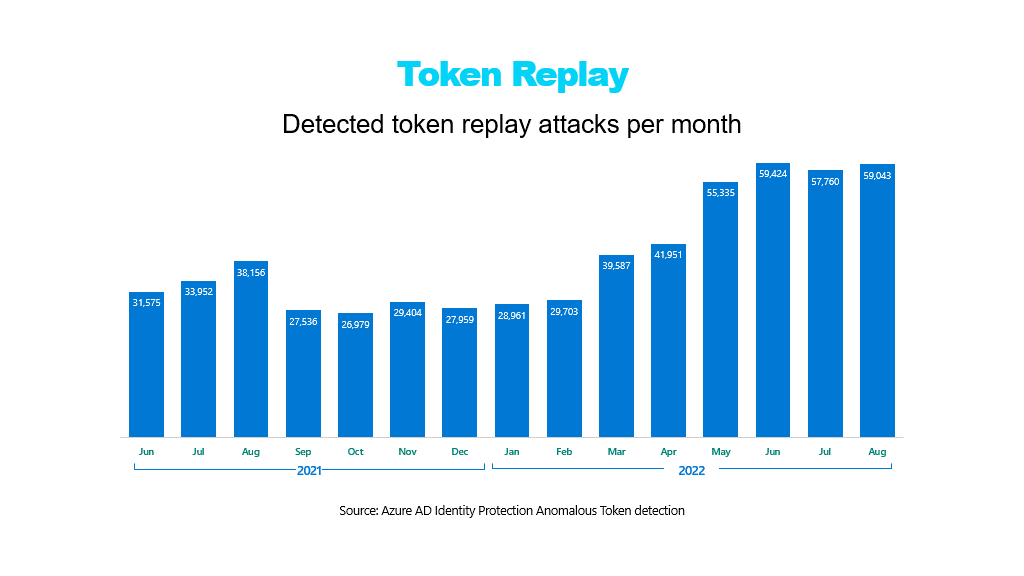
Determined attackers are using malware to steal tokens from devices—
Another bypass attack is OAuth consent phishing. This is where someone tricks an existing user into giving an application permission to access on their behalf. Attackers send a link asking for consent (“consent phishing”) and if the user falls for the attack, then the app can access the user’s data even when the user is not present. Like other attacks in this category, they are rare but increasing. We strongly recommend inspecting what apps your users are consenting to and limiting consent to applications from verified publishers.
Infrastructure compromise
As you get more effective at using identity to secure your organizations and build your Zero Trust policies, advanced attackers are attacking identity infrastructure itself—
We are working hard to strengthen hybrid and multicloud detections and build automated protection for specific indicators that attackers are moving against identity infrastructure. Critically, because of the incredible difficulty of protecting on-premises deployments from malware, lateral movement, and emerging threats, you should reduce your dependencies on on-premises infrastructure, shifting authority to the cloud where possible. You should specifically isolate your cloud infrastructure from your on-premises environment. Finally, it is critical to partner closely with your security operations center (SOC) to make sure that privileged identity administrators and on-premises servers win special scrutiny. And because today’s sophisticated adversaries will look for any gap in your security, securing user identities also means protecting non-human identities and the infrastructure that stores and manages identities as well.
The rogue wave: Attack velocity and intensity
Our team assists with hundreds of significant cases every year, and one of the most critical issues we see is the difficulty of keeping up with increasing volumes and intensity of attacks. Whether it is assisting customers who are running Windows Server 2008 Domain Controllers or the customers still struggling with multifactor authentication rollout, the rapid pace of attacker innovation is hard to meet for organizations with the tremendous budget, resources, hiring, and political pressure facing them—
Our team is committed not just to reducing costs associated with identity attacks, but to massively reducing the investments required to get and stay secure. This is the common thread that runs through our many investments—
As you invest in identity security, we encourage you to invest in mechanisms that allow your organization to be agile—
Fair winds and following seas in 2023
Whether you’re an admin at a major company or launching a startup from your garage, protecting user identities is crucial. Knowing who is accessing your resources and for what purpose provides a foundation of security upon which all else rests. For that reason, it’s imperative to do everything possible to strengthen your identity posture today. The challenges are significant, but defensive strategies and technology are there to help.
If I may be so bold as to propose some New Year’s resolutions for your identity security efforts:
- Protect all your users with multifactor authentication, always, using Authenticator, Fast Identity Online (FIDO), Windows Hello, or CBA.
- Apply Conditional Access rules to your applications to defend against application attacks.
- Use mobile device management and endpoint protection policies—especially prohibiting running as admin on devices—to inhibit token theft attacks.
- Limit on-premises exposure and integrate your SOC and identity efforts to ensure you are defending your identity infrastructure.
- Bet hard on agility with a cloud-first approach, adaptable authentication, and deep commitments to automated responses to common problems to save your critical resources for true crises.
Each of these recommendations has value in and of itself, but taken together, they represent an approach to defense-in-depth. Defense-in-depth encourages us to assume that any single control might be overcome by an attacker, so we have multiple layers of defense. In the recommendations listed in this blog, a user with perfect authentication should never be compromised, but we layer in endpoint protection, SOC monitoring, automated responses, and posture agility assuming that no one control is adequate.
To learn more about how you can protect your organization, be sure to read Joy Chik’s blog, Microsoft Entra: 5 identity priorities for 2023. If you’re interested in a comprehensive security solution that includes identity and access management, extended detection and response, and security information and event management, visit the Microsoft Entra page, along with Microsoft Defender for Identity and Microsoft Sentinel, to learn how this family of multicloud identity and security products can protect your organization.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.


